Azure Red Team Specialist [AzRTS]
The Azure Red Team Operations course is designed to equip cybersecurity professionals with the skills, techniques, and practical knowledge required to simulate real-world attacks in Microsoft Azure environments.
- Understand the Azure cloud architecture from an attacker’s perspective
- Identify misconfigurations in Entra ID, ARM, and M365
- Simulate real-world attack chains targeting Azure environments
- Perform identity-based attacks against Microsoft cloud services
- Conduct lateral movement between on-premises and cloud infrastructure
- Map attacks to the MITRE ATT&CK Cloud Matrix
- Understand modern cloud threat research methodologies
Offer Price: $49 ($̶𝟷̶𝟺̶𝟿̶)
- Azure tenant reconnaissance and cloud attack surface discovery
- Identity enumeration and privilege mapping within Microsoft Entra ID
- Authentication abuse and token manipulation techniques
- Role-based access control (RBAC) misconfiguration exploitation
- Managed identity abuse and service principal attack paths
- Microsoft Graph API reconnaissance and permission abuse
- Conditional access policy evasion and identity control bypass techniques
- Microsoft 365 service enumeration and cloud data access tradecraft
- Cross-service identity pivoting between Azure and Microsoft 365
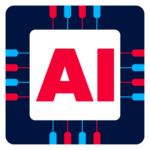
- Hybrid identity attack paths involving Entra ID Connect
- On-premises to cloud and vice-versa lateral movement techniques
- Persistence mechanisms within Azure identity and resource layers
The course content is divided across 5 sections listed below:
Module 1: Introduction to Azure
- Overview of Azure Cloud
- Azure Architecture for Red Teaming
- Control Plane vs Data Plane
- Authentication Flow for Microsoft Graph API
- Cyber Kill Chain in Azure
- Red Team Objectives in Azure
- Attack Lifecycle in Azure
- Azure Threat Research Matrix
- Mapping Azure attacks to the MITRE ATT&CK Cloud Framework
Module 2 : Microsoft Entra ID (Azure AD)
- Fundamentals of Entra ID
- Overview of Microsoft Entra ID
- Identity Types in Entra ID
- Administrative Units
- Roles & Administrators
- Identity Governance and PIM
- Conditional Access Policies
- Entra ID Connect and Hybrid Identity
- Red Team Operations in Entra ID
Module 3: Azure Resource Manager (ARM)
- Fundamentals of Azure Resource Manager
- Overview of Azure Resource Manager
- Managed Identities
- Resource Providers
- Azure Services
- Automation Accounts
- Red Team Operations in ARM
Module 4: Microsoft 365 (M365)
- Fundamentals of Microsoft 365
- Overview of Microsoft 365
- Core Services
- Authentication Mechanisms
- Administrative Roles
- Red Team Operations in M365
Module 5: Lateral Movement
- On-premises to Entra ID
- Entra ID to On-premises
Pre-requisites
- Basic understanding of cloud computing concepts
- Familiarity with Azure fundamentals
- Basic knowledge of Active Directory and identity management
- Basic knowledge of privilege escalation and lateral movement
- Fundamentals of penetration testing or red teaming
- Understanding of attack frameworks like MITRE ATT&CK
- Experience with Linux and Windows environments
- Familiarity with PowerShell or scripting
- Prior exposure to cloud security or DevOps environments
Target Audience:
- Red Teamers & Offensive Security Professionals
- Security Researchers
- Pentesters
- Detection Engineers wanting attacker insight
- Identity & IAM Security Professionals
- Cloud Security Engineers
- Advanced Blue Team members seeking adversary simulation knowledge
Premium Version
Azure Red Team Specialist (Az-RTS)
$149 $49
Top features:
- 300 + pages PDF
- 15+ hours HD videos
- Lifetime Course Access
- 15+ Flag-Based Challenges
- Unlimited Challenge Attempts
- 30 Days AzRTS Exam Lab Access
- Technical Support
F.A.Q
This course is designed for cybersecurity professionals who want to understand offensive security techniques in Microsoft Azure environments. It is ideal for:
- Red Teamers
- Penetration Testers
- Cloud Security Engineers
- Threat Hunters
- SOC Analysts
- Security Researchers
- DevSecOps Engineers
Anyone responsible for securing or assessing Azure environments will benefit from this training.
Basic familiarity with cloud computing concepts is recommended, but deep Azure expertise is not required. The course begins with foundational topics such as Azure architecture, Microsoft Entra ID, and Azure Resource Manager before moving into offensive security techniques.
Yes. This course includes practical lab exercises in a dedicated Azure lab environment. Participants will simulate realistic attack scenarios involving identity abuse, privilege escalation, and lateral movement across cloud services.
The course focuses on offensive security techniques targeting key Microsoft cloud platforms, including:
- Microsoft Entra ID
- Azure Resource Manager
- Microsoft 365
Students will also explore hybrid identity scenarios involving on-premises infrastructure and cloud environments.
By completing the course, participants will gain practical knowledge in:
- Azure attack surface discovery
- Identity-based attack techniques
- Privilege escalation in Azure environments
- Token and authentication abuse
- Microsoft Graph API reconnaissance
- Cloud persistence techniques
- Hybrid identity attack paths
- Cloud lateral movement techniques
The course also maps techniques to the MITRE ATT&CK Cloud Matrix to help students understand modern cloud adversary behavior.
Yes. A dedicated module focuses on hybrid attack paths, including:
- On-premises Active Directory → Azure compromise
- Azure → On-premises lateral movement
- Identity synchronization abuse through Entra ID Connect
These scenarios reflect real-world enterprise environments where cloud and on-premises systems coexist.
A dedicated Exam Lab environment will be provided for participants to complete the course assessment and validate their skills.
For additional hands-on practice and to replicate the lab scenarios independently, participants are recommended to have their own **Microsoft Azure subscription.
The course typically takes 30–35 hours to complete, depending on the learning format and time spent on lab exercises.
Yes. Participants will receive a course completion certificate after successfully finishing the training.
This course is best suited for intermediate-level cybersecurity professionals. Participants should have a basic understanding of:
- Networking concepts
- Identity and authentication systems
- Security testing or red team fundamentals
Most Azure courses focus on defensive configurations and administration. This course takes an attacker’s perspective, teaching participants how adversaries exploit misconfigurations, abuse identity systems, and move laterally within Azure environments.
CWL follows a strict no-refund policy once access is granted. Please review the course details carefully before purchasing.
If your query isn’t listed here, feel free to contact [email protected].