Stealth Cyber Operator [CSCO]
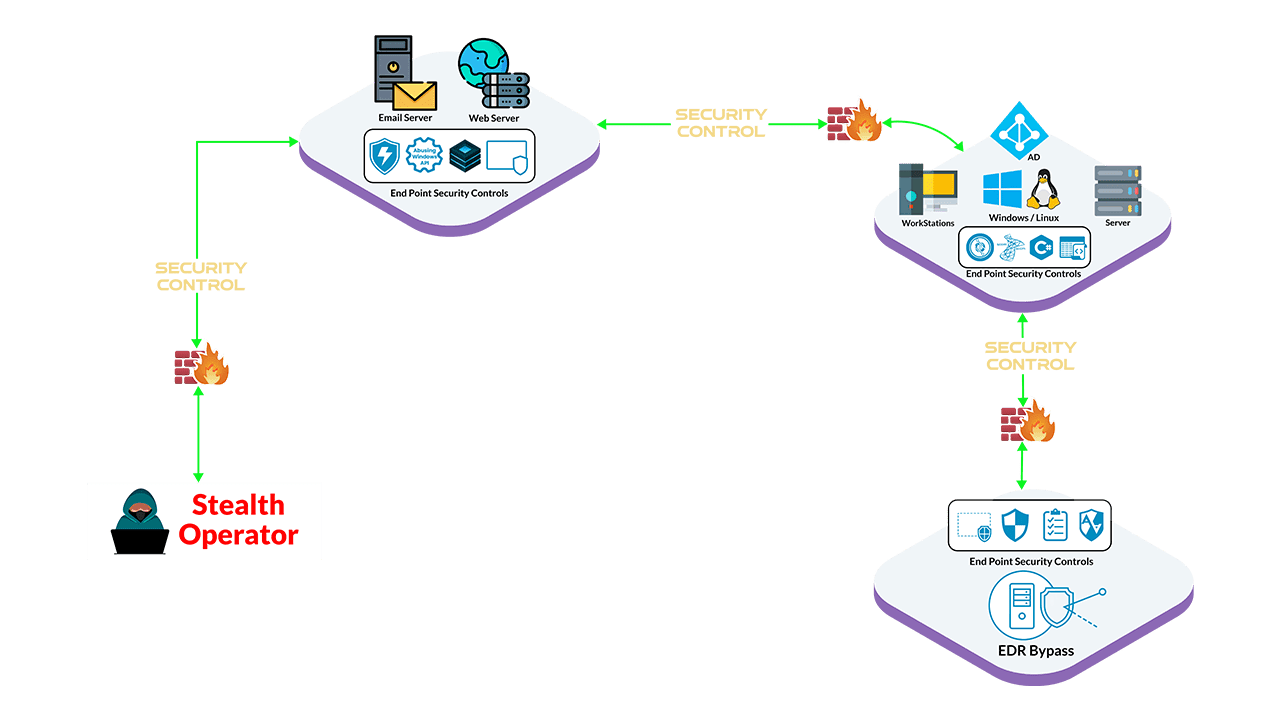
- Red Team Resource Development [Infra Setup]
- Abuse improperly placed and mis-configured security controls in infrastructure
- Trade-craft development for Offensive Operations
- Resource abuse using Windows APIs, C, C++ & Csharp
- Utilizing Trade-craft for Red Teaming in Hardened Environment
- Leveraging Endpoint Security Controls (AV, EDR) & so much more…
The courses contents are divided across 4 sections listed below:
Red Team Resource Development
- Enterprise Security Controls Architecture
- Bypassing / Circumventing Initial Access Defenses
- Red Team Infrastructure Development
- Initial Access by Abusing Enterprise Applications
- Custom scripts / code for Operational Security
Trade-craft Development for Offensive Operations
- Hands-on offensive trade-craft development (C# & Windows API)
- Fully Undetectable (FUD) payload creation strategies
- Understanding Microsoft & Linux Based Security Controls
- Defense Evasion Strategies for malware development
Utilizing Trade-craft for Red Teaming in Hardened Environment
- Microsoft based security controls defense evasion
- Circumventing Host & Network based security controls
- Interesting Cross Forest Trust abuse scenario
- Custom ways for credential access in windows & Linux boxes
- Real-World Engagement case scenarios
Blinding Endpoint Defenses [Explicit Edition]
- ETW & EDR Basics
- Deep Diving into endpoint security internals
- Evasion Strategies & Exercises
- FUD ETW & EDR Bypasses
- Enterprise Security Controls Lab Access
Cyber Range Lab Highlights
- Stealth-Ops Enterprise Simulation Lab
- Stealth-Ops Completion Certificate + Exam Badge
- Hands-on Endpoint Defense Evasion Exercises
- StealthOps VM containing custom code snippets
- Study Materials : 200+ Pages PDF
- Setup your own OPSEC safe Red Team Infra
Pre-requisites
Following are the requirements:
- Fair Knowledge of Networking and Web Technology *
- Familiarity with command line interface
- Familiarity with virtualization technologies
- Basics of Penetration testing methodology
- An Open mind 😊
* Basic coding knowledge in C is good but not mandatory.
Target Audience
Targeted Audience may include the following group of people:
- Penetration Testers / Red Teams
- System Administrators
- Malware Developers
- SOC analysts
- Threat Hunting Team
- Last but not the least, anyone who is interested in strengthening their offensive and detection capabilities
Premium Version
Stealth Cyber Operator [CSCO]
$599
Top Features:
- 150+ pages PDF & Lab Write-ups
- 12 Hrs+ Training Recorded Videos
- 30 Days Challenge Lab
- Access to Customized VM including custom scripts
- Earn Verified Accredible Badge
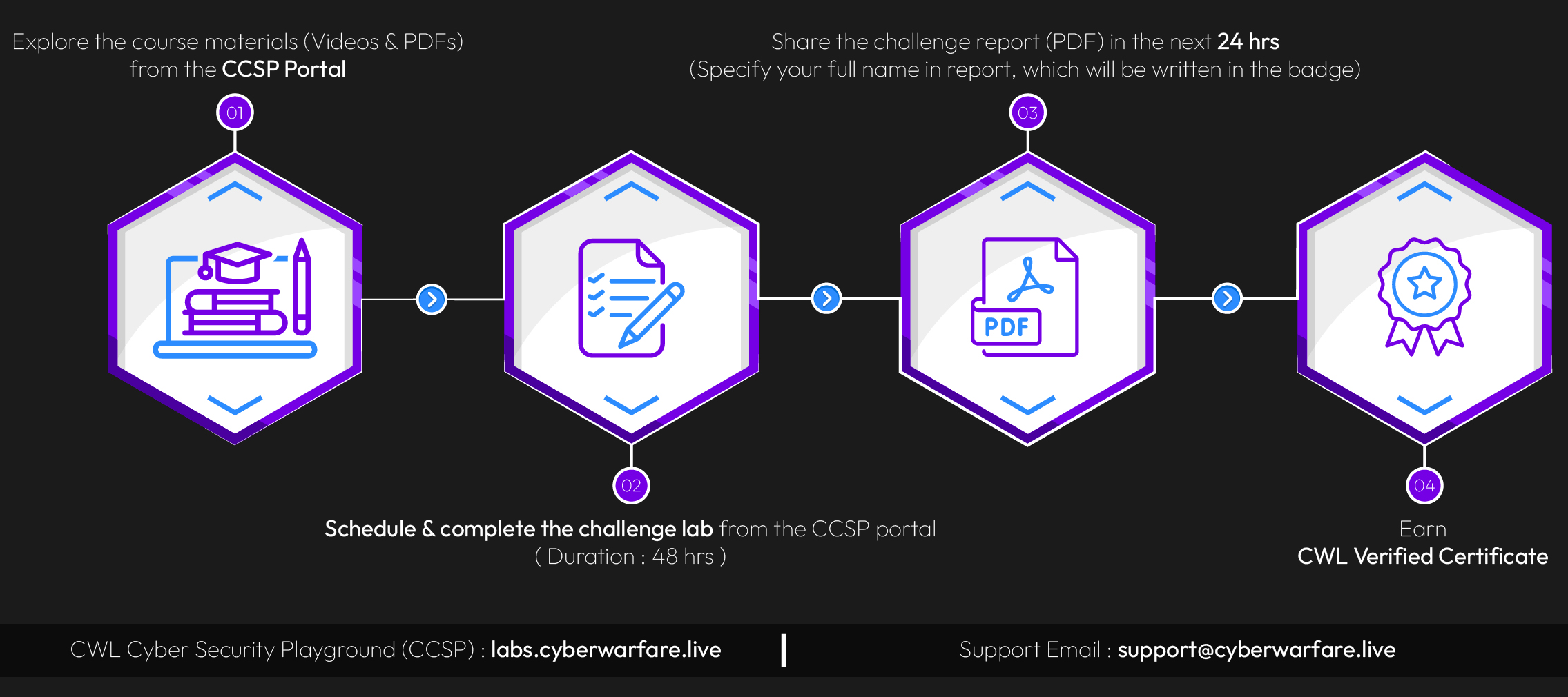
Choose your journey and earn the Certified Stealth Cyber Operator Certification today
F.A.Q
- 150+ pages PDF & Lab Write-ups
- 12 Hrs+ Training Recorded Videos
- Challenge Lab of 48 Hrs
- Access to Customized VM including custom scripts
- Earn Verified Accredible Badge
Yes, After purchase you will get the life-time access.
The duration of the Stealth Cyber Operator [CSCO] course may vary based on individual learning pace, but on average, it takes around 20 Days to complete.
The Stealth Cyber Operator [CSCO] course is delivered On-Demand Mode which includes online video lectures, practical hands-on exercises, and virtual labs.
The Stealth Cyber Operator [CSCO] exam is a practical hands-on assessment that evaluates the student’s ability to perform real-world red teaming engagements. Students are given specific scenarios and objectives to accomplish within a specified timeframe. The exam is evaluated by experienced instructors.
No, we only activate lab access upon request, which will be provided within 48 hours.
Upon completing the Stealth Cyber Operator [CSCO] course and obtaining the certification, you can pursue various career opportunities such as:
- Red Team Manager / Lead / Operator
- Lead Penetration Tester / Senior Security Consultant
- Adversary Simulation Specialist / Expert
Yes, our support team is there for you 🙂
Refunds for premium subscription will NOT be provided until and unless cleared by our sales team.
Please email [email protected] for detailed clarification
Our Customer Say It Best

Course: CSCO
Again it was great adventure during which I learnt new interesting techniques which next will be used in the LAB for which I'm also waiting.
Thank you Team for excellent work from your side!

Course: CSCO