Offensive Cyber Operations with AI (OCO-AI)
- Weaponize LLMs and Autonomous Agents Across the Full Cyber Kill Chain
- Build AI-Driven OSINT Pipelines, MCP-Integrated C2 Infrastructure, and Agentic Recon Operators
- Operate Claude and Local Uncensored-LLMs for Binary Analysis, AD Exploitation, and Spear-Phishing Automation
- 7 Adversarial Modules fully mapped to MITRE ATT&CK for Enterprise
- Every TTP is operationally viable, purpose-built for real-world red team engagements
- End-to-End AI-Augmented Kill Chain Operations: From OSINT to Post-Exploitation
- Autonomous Recon Agents with Live Target Interaction Using Claude and Local LLMs
- Threat Modeling Any Technical Stack with AI-Generated ATT&CK-Mapped Attack Scenarios
- MCP-Integrated C2 Command Execution via Natural Language Against Live Infrastructure
- LLM-Powered Binary Reverse Engineering with Ghidra MCP and Decompilation Interpretation
- AI-Driven AD Pathfinding and BloodHound-Augmented Lateral Movement Planning
- Spear-Phishing OSINT Pipelines with n8n Workflow Automation and Context-Aware Payload Generation
- Uncensored Local LLM Operations with Dolphin-Llama3 for Unrestricted Offensive Workflows
- Custom Python MCP Server Development for Offensive Tool Integration and C2 Wrapping
- LOLBIN Abuse and Win Internals Exploitation Guided by AI-Assisted Binary Analysis
Attack Simulation
- Uncensored LLM Deployment and Operational Model Selection for Offensive Use Cases
- AI-Driven Threat Modeling with Automated Attack Surface Analysis and Architecture Diagramming
- CTI and DFIR Report Ingestion: Automated ATT&CK Technique Extraction and Scenario Synthesis
- AI-Synthesized Red Team Scenario Generation: Initial Access, Persistence, and Lateral Movement Planning
- Autonomous Spear-Phishing Pipeline: Employee Enumeration, Context Enrichment, and Payload Personalization
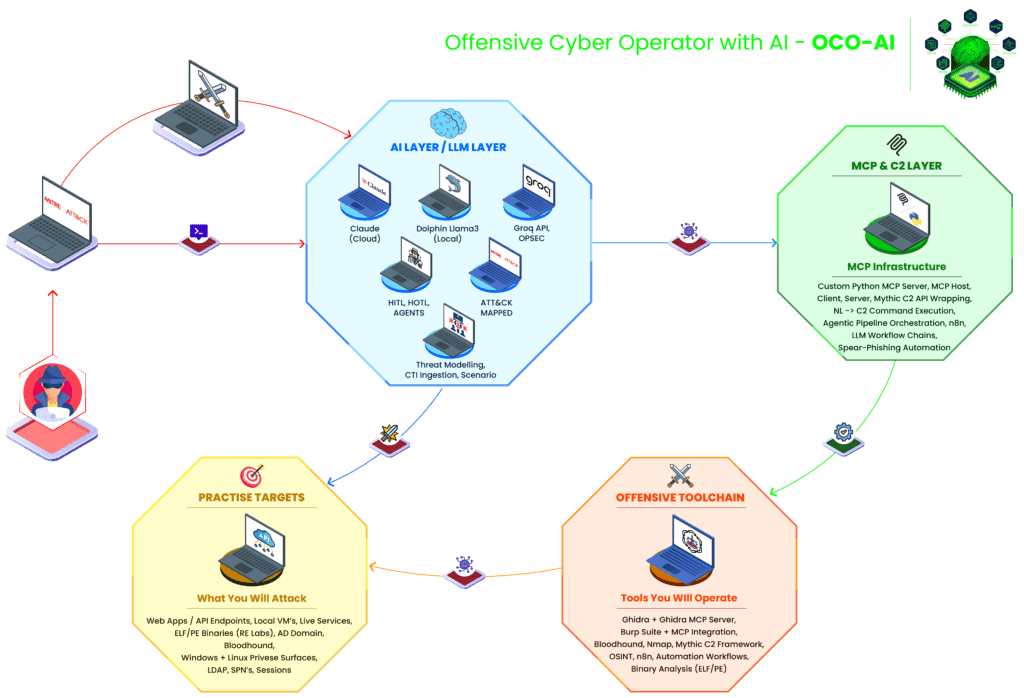
AI Infrastructure & Agentic Tooling
- Model Context Protocol (MCP) Architecture — Host, Client, Server
- Custom Python MCP Server Development for Offensive Tooling
- Natural Language to C2 Command Execution via Mythic API Wrapping
- Claude + Local LLM Operational Setup with OPSEC Boundaries
- Human-in-the-Loop vs Human-on-the-Loop Operational Control Models
Autonomous Reconnaissance & Initial Access
- AI-Driven Employee Enumeration and Spear-Phishing OSINT Pipelines
- Custom n8n + LLM Workflow Automation for Context-Aware Phishing Preparation
- Autonomous Network Recon Agents: Nmap Execution, Service Fingerprinting, CVE Surface Mapping
- AI-Assisted Web Attack Surface Discovery: Subdomain, Endpoint, and Parameter Enumeration
- Burp Suite MCP Integration for AI-Guided Request Analysis
Binary Analysis & Exploitation
- Ghidra MCP Integration for LLM-Augmented Decompilation Interpretation
- AI-Assisted Vulnerability Identification and Exploitation Path Generation
- LOLBIN Abuse Vector Discovery via Trusted Binary Analysis
- Win Internals: Custom Field Weaponization and VBScript Code Execution Primitive
- Source Code Reconstruction and Script Generation from Decompiled Output
Red Team Operations & Post-Exploitation
- AI-Assisted Privilege Escalation Analysis — Windows and Linux Attack Surfaces
- LDAP Enumeration, SPN Discovery, and Session Analysis with AI-Driven Interpretation
- BloodHound Pathfinding — Shortest Path, Stealth Path, and Credential Requirement Mapping
- OPSEC-Safe Lateral Movement Planning with AI Decision Support
Pre-requisites
The following are the requirements:
- 16 GB+ RAM system capable of running a hypervisor (VMware Workstation preferred)
- Basic understanding of networking, Active Directory concepts, and API interactions
- Foundational scripting ability in Python or JavaScript
- No prior AI/LLM experience required, offensive mindset is the only prerequisite
Target Audience:
Designed specifically for practitioners operating at the intersection of AI and offensive security:
- Red Team Operators integrating AI tooling into live engagements
- Penetration Testers looking to accelerate recon, analysis, and reporting with LLMs
- Cybersecurity Researchers building autonomous offensive tooling and agentic pipelines
- Security Engineers exploring AI-driven automation across the attack lifecycle
- Advanced students pursuing AI-augmented adversary simulation tradecraft
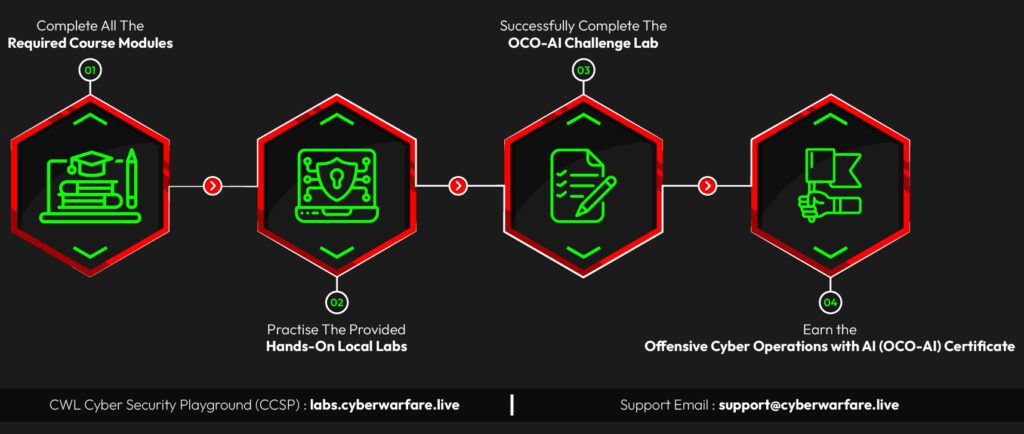
To earn the CWL Offensive Cyber Operations with AI (OCO-AI) Certificate, participants must:
Premium Version
Offensive Cyber Operations with AI (OCO-AI)
$99 $29
Top features:
- 100+ Pages Premium Course Material
- 15+ Hands-on Offensive Labs Across 7 Adversarial Modules
- 20+ Practical Exercises with 75+ Pages Walkthrough
- Unlimited Exam Attempts
- CWL Verified OCO-AI Certificate + Accredible Badge
- Access to CWL Red Team Community (Discord)
F.A.Q
The release dates are set to 30th May 2026 along with exam scenarios and fully obtainable certifications.
Study materials and labs are available via the CWL Labs Portal (CCSP)
https://labs.cyberwarfare.live
Once enrolled, you can access the video lectures, PDF materials, and lab environments using your registered email.
Yes. You will have lifetime access to the course materials and recorded content. Lab environments may receive updates periodically.
The estimated completion time is 30 Days, depending on your experience level and learning pace.
After completing the course, learners may pursue roles such as:
- Red Team Operator
- Offensive Security Engineer
- AI Security Researcher
- Security Automation Engineer
CWL follows a strict no-refund policy once course access has been granted.
If your query isn’t listed here, feel free to contact [email protected].